Beckman Coulter's Remisol Advance - Security Advisory MARBAS-22-001
Affected Product: Beckman Coulter Remisol Advance v2.0.12.1 and below
Vulnerability Type: Insecure Permissions & Privilege Escalation
Root Cause: The permissions set by Remisol Advance V2.0.12.1 and below on install for six running services allows for non-privileged users to overwrite and/or manipulate executables and libraries which run as the elevated SYSTEM user on Windows.
Affected Components and corresponding CVEs:
- CVE-2022-26235: Normand Message Server
- CVE-2022-26236: Normand Remisol Advance Launcher
- CVE-2022-26237: Normand ViewerService
- CVE-2022-26238: Normand Service Manager
- CVE-2022-26239: Normand License Manager
- CVE-2022-26240: Normand Message Buffer
It's no secret that healthcare technology offers a buffet of information to would-be attackers. It's amazing how many systems, vendors, and technologies you've never even heard of are burdened with rich sets of information which these unheard entities are then entrusted to. On top of all of this, there's a consumer expectation that these systems are protected or at least given attention when they have serious problems.
Expectations are funny things.
This disclosure specifically deals with the software product Beckman sells as LIMS middleware Remisol Advance. Remisol is supposedly doing the following according to Beckman's marketing materials:
REMISOL Advance is a leading middleware solution for today’s clinical laboratories, bridging laboratory information systems (LIS) and instrumentation. It helps drive improved operational efficiency within and across the laboratory network through process automation and standardization. The enhanced capabilities of dashboards provide real-time insights into operations and fast access to key metrics for more informed decision-making.
We've opened the following CVEs for this disclosure which lead to privilege escalation:
The vulnerabilities are simple enough Windows vulnerabilities related to incorrect permissions on installed services. Remisol Advance runs these six services with the SYSTEM account when installed. Also, when installed, the files where the services are initialized are something all users can write to. A user could kill the process which is running the service, install malware, and restart the service to take advantage of the SYSTEM account.
The fix is simple: correct the permissions so that every user cannot overwrite the services and therefore make themselves a super admin on the local Windows host.
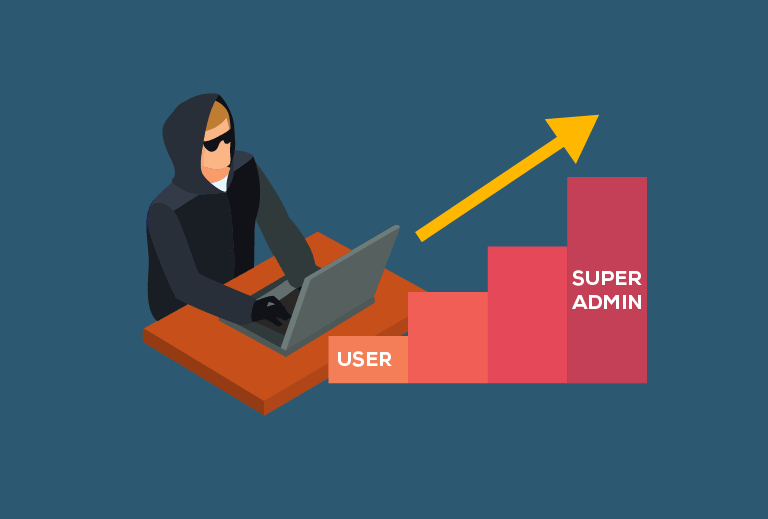
Movin' on up thanks to Beckman Coulter!
The biggest concern is that this software is installed on Windows workstations which are often placed in easy to access areas of the hospital. Think lab stations where a phlebotomist might take a blood sample, also - in most chemistry, hematology and microbiology labs. Labs are usually running around the clock processing samples and workstations are usually logged in and ready to take data from users. Don't believe me? Do a google search for an example - think something like this.

Or this...
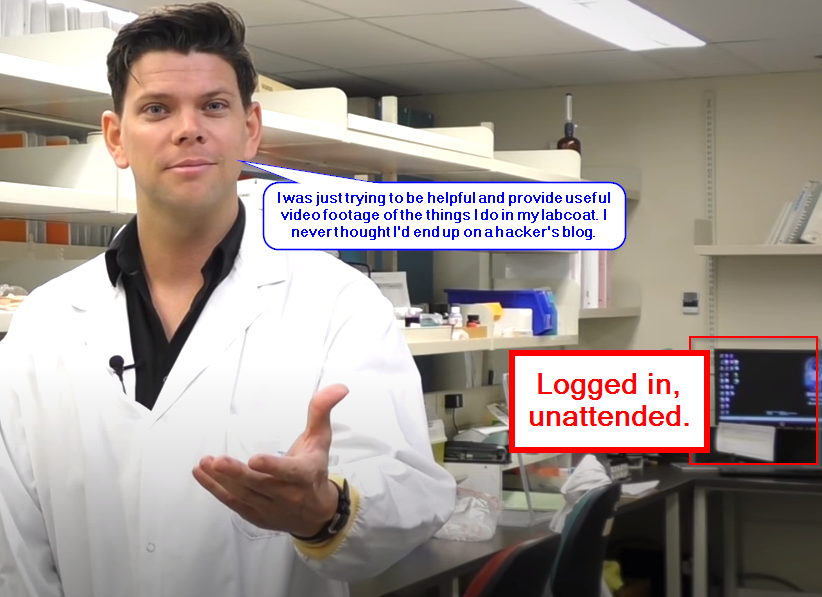
I think after googling these I'm on some list now....
This is commonplace, and as such these workstations are typically locked down with controls that account for malicious users. These controls can be circumvented when an attacker takes advantage of these vulnerabilities. As stated, the services allow for the overwriting of libraries and executables which lead to privesc. Per the CVE disclosures:
The default privileges for the running service *Service name here, because there's six* in Beckman Coulter Remisol Advance v2.0.12.1 and prior allows non-privileged users to overwrite and manipulate executables and libraries. This allows attackers to access sensitive data.
This sensitive data is PHI.... and administrative control over the system and future inputs. The combination between easy physical access of systems and really dumb (and very preventable) vulnerabilities is a perfect storm of several abuse cases.
Although, we're talking about physical access though. If you're lucky enough to be network adjacent, you can look forward to default passwords configured for the highest levels of access enabled by default.
Not disclosed as a CVE, we found documents while attempting to authenticate to the software directly using usernames and passwords. Using simple Google searches, we found published materials on Beckman's website 8 years ago which gives users super admin rights into the software itself. From what was observed - the vendor likely installs this middleware and then leaves it with defaults intact.

8 years old is a great age to be when you're a human - not so much if you're a password.
What's interesting about these security findings is that they're just so elementary that they should have been caught by basic vulnerability scanners and/or penetration testing if Beckman had even decided to do that sort of thing on their own products. So, if you're out there Beckman - we have some advice for you:
- Don't install customers with your software using published default passwords which give super admin privileges. Advise your current customer to change their passwords because this is likely everywhere.
- Don't use SYSTEM to run services which you then grant everyone the ability to modify the files - which in turn gives them the ability to change said files.
- Do basic security work in assessing your systems in the future. You're a five-billion-dollar company. Shape up.
If you're a customer of Beckman Coulter, my apologies but you'll need to do the following if they haven't helped you.
- Change default passwords on any Remisol Advance or Beckman product with the knowledge that they publish and use default passwords for customer products.
- Monitor systems using the Remisol Advance middleware for unusual behavior, especially related to their services which apparently need to run with full administrator privileges. Possibly lock down those folders if you have a decent team who can harden and then validate access to those files.
- Ask Beckman to be better with their security and ask specific questions about what they're doing to improve.
Thanks for checking out the blog - till next time. :-)
-Marbaṩ
9/12/22 Edit: Added one more service - originally publishing five when there were six in total. Also cleaned up content so it's easier for MITRE to consume.